tty= teletypewriter
Ctrl+Alt + F1 =tty1
Ctrl+Alt + F2 =tty2
.
.
Ctrl+Alt+F7= graphic
Description of Command
$apropos file
See manual
$ man file
where we are?
$ which ls
what is in root
$ ls /
show files in list
$ls -l
show the content of directory
$ls -lR
. current directory
.. parent directory
~ user’s home folder
Editors
nano , vim ,vi
$ nano FileName
$ vi FileName
exit : escape :q
To create file
$ touch filename
To see inside file
$ cat filename
To copy
$ cp sourceDirectory Destination
$ cp myfile2 myfile3 Documents // copy to two destinations
To remove file
$ rm myfile
Give list of the files starts with a
$ ls a*
give list of the files starts with three character
$ls ???
link files together
ln users.txt Document/list.txt
find a file larger than 10M
$ find +size +10M
write some text in file
$echo “more information” > output.txt
$ ls > homedir.txt
Use Pipe
$ cat homedir.txt | wc
// count file text
compare files
$diff -y text1.txt text2.txt
$ diff -u text1.txt text2.txt
compare binaries files
$ cmp text1.txt text2.txt
Archives and Compression
$tar -cf doc.tar listoffiles
$tar -tf doc.tar //read
$tar -xf doc.tar extractdistination
Zip file1 file2 …
unzip myfiles.zip -d unzip //create foldername unzip to extract
Find with grep
$ cat users.txt | grep -E “[A-M][m-z]”
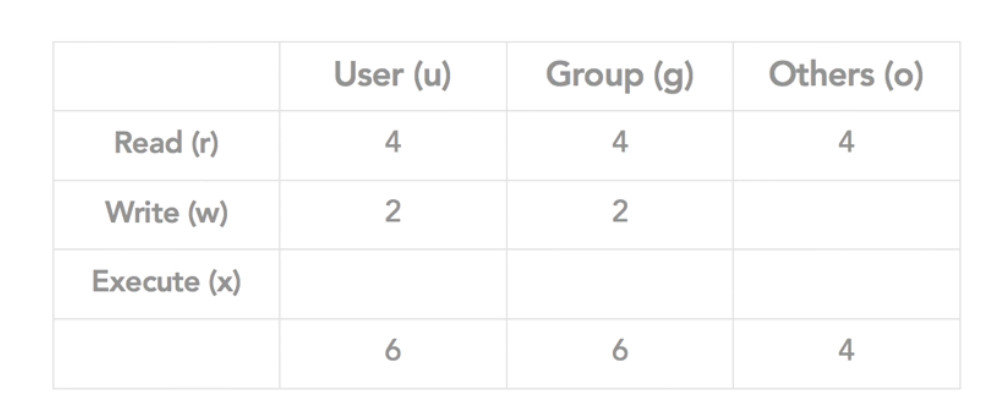
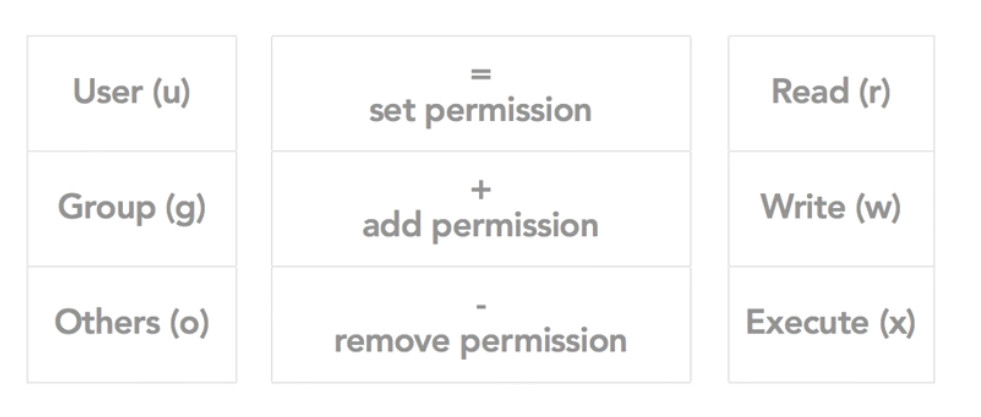
change permission
$ chmod 600 myfile
$ chmod ugo+rwx myfile
change currnet user to root user
$sudo -s
#
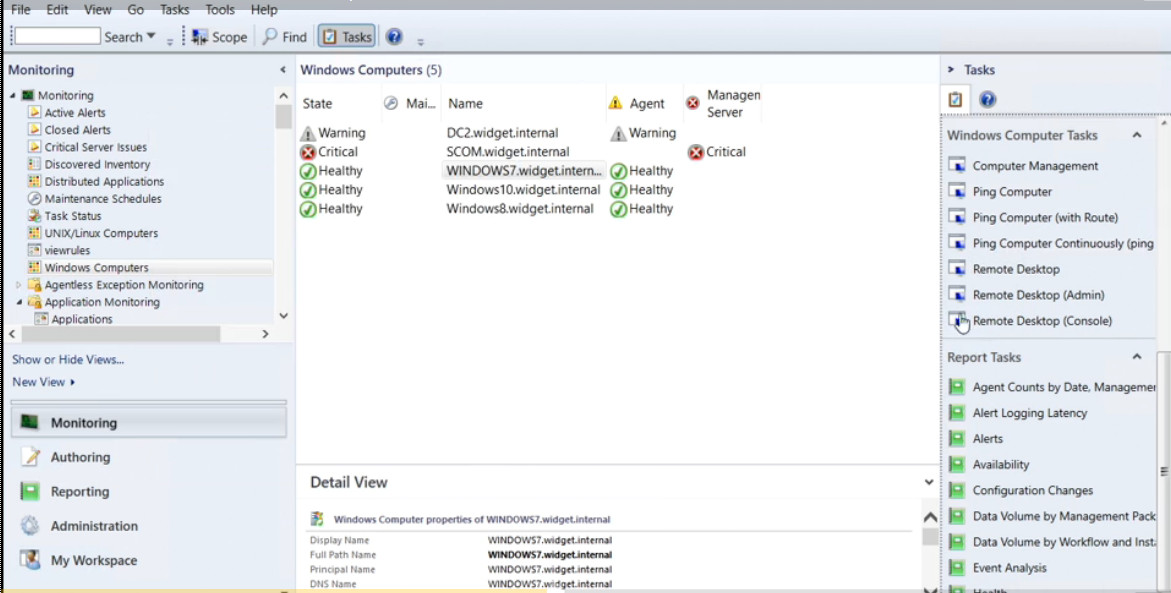
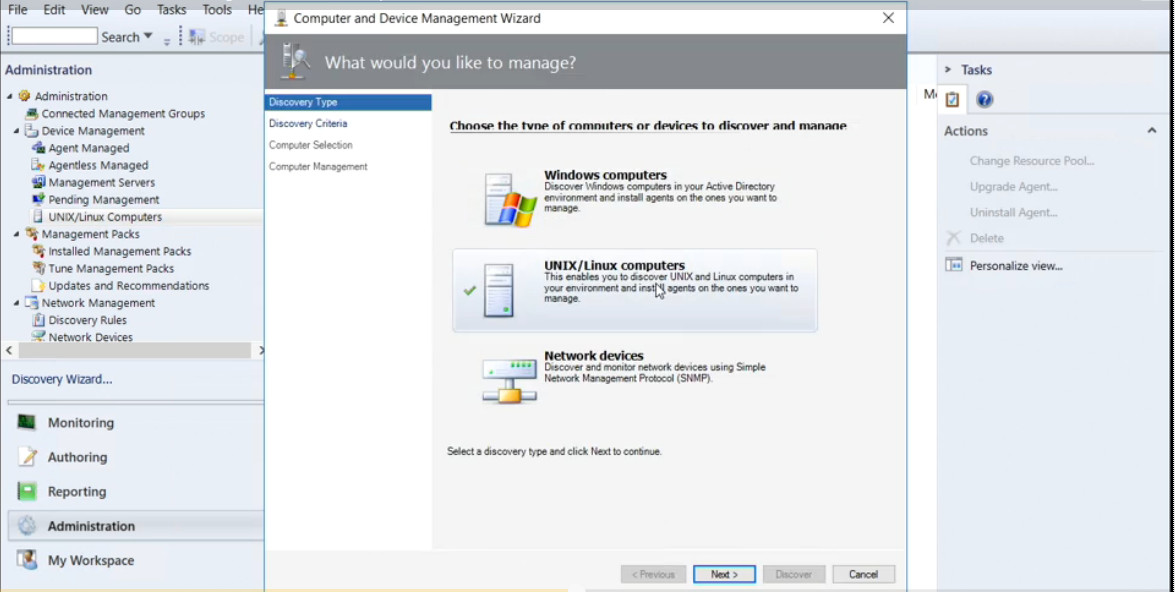
SSH
$sudo apt install openssh-server
to connect from another system: ssh user@ip
SFTP
$ get file3
$ put file3
SCP
Secure Copy Protocol
remote component user@host:path-to-file
$scp file4 hrt@192.168.3.10:/Documents
Packages update
sudo apt-get update
sudo apt-get upgrade
Enable Firewall
ufw enable
ufw allow 22/tcp
Disable Firewall
ufw disable
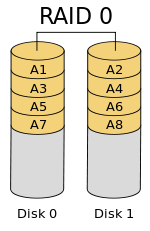
dd if=source of=destination // copy large – cloning
ps //show process
ps aux | grep “evol”
ifconfig
apt-get install ….
ip address add 192.168.99.37/24 dev eth0